8i | 9i | 10g | 11g | 12c | 13c | 18c | 19c | 21c | 23c | Misc | PL/SQL | SQL | RAC | WebLogic | Linux
Apache : Reverse Proxy Configuration
A reverse proxy can act as a gateway service allowing access to servers on your trusted network from an external network.
There are a number of ways to achieve this, but this article discusses how to configure a reverse proxy using Apache virtual hosts. It is assumed you already have a working Apache installation. If not, you can see how to install Apache on Linux here.
Related articles.
- Linux HTTP Server Configuration
- Apache Tomcat Installation on Linux
- Apache Monitoring using mod_status (server-status)
- NGINX : Reverse Proxy Configuration
- Let's Encrypt - Free Certificates on Oracle Linux (CertBot)
Introduction
Using a reverse proxy is a simple and convenient approach to allowing access to servers on your trusted network from external networks, such as the internet.
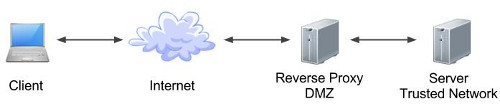
Much of its appeal comes from the fact it allows all your servers to remain hidden from the external networks and the user community. The diagram below shows a simple architecture that could be employed to achieve this. Of course, there are an almost limitless variety of configurations possible depending on your requirements and the products being used.
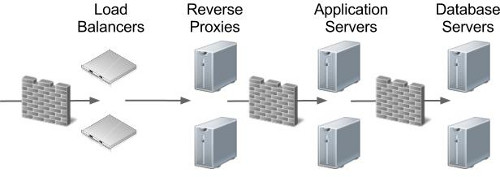
Reverse proxies provide a number of benefits in terms of security and maintenance, including the following.
- The obvious point is none of your application or database servers are exposed to external networks directly, which is a good starting point when trying to build a secure solution.
- URLs presented to users can be "pretty", rather than containing specific machine names, ports and long paths. A simple redirect would still expose the true URL, while a reverse proxy completely hides it from the user.
- Following on from the previous point, users bookmark URLs. If that bookmark contains a specific machine name, then no matter how resilient you try to make your solution, they will go to their bookmark and think your site it down. Separating them from the physical implementation of your services make your apparent availability better.
- From a security perspective, the less architectural information you expose to the outside world, the better. If hackers are presented the actual machine names and ports that are running a service, it makes it significantly easier for them to attack those services.
- The fact the URLs no longer point directly to actual machines enables dramatic architecture changes to be hidden from users. A simple configuration change within the reverse proxy can direct all the workload to a new set of servers.
HTTP Reverse Proxy
The "ProxyPass" and "ProxyPassReverse" parameters are used to tell Apache how to proxy requests. They require the "mod_proxy.so" and "mod_proxy_http.so" Apache modules, which are loaded by default in RHEL5 and RHEL6, but check the following lines are uncommented in the "/etc/httpd/conf/httpd.conf" file to make sure.
LoadModule proxy_module modules/mod_proxy.so LoadModule proxy_http_module modules/mod_proxy_http.so
In the following example, the "my-app-1.example.com" and "my-app-2.example.com" URLs resolve to the IP address of the reverse proxy server. The "/etc/httpd/conf/httpd.conf" entries below use named virtual hosts to proxy the two URLs to the appropriate internal server(s).
ProxyRequests Off
NameVirtualHost *:80
<VirtualHost *:80>
ServerName my-app-1.example.com
ServerAlias my-app-1
ErrorLog /var/log/httpd/my-app-1-error_log
TransferLog /var/log/httpd/my-app-1-access_log
ProxyPass / http://app-server-1.localdomain:7002/
ProxyPassReverse / http://app-server-1.localdomain:7002/
</VirtualHost>
<VirtualHost *:80>
ServerName my-app-2.example.com
ServerAlias my-app-2
ErrorLog /var/log/httpd/my-app-2-error_log
TransferLog /var/log/httpd/my-app-2-access_log
ProxyPass / http://app-server-1.localdomain:7004/
ProxyPassReverse / http://app-server-1.localdomain:7004/
</VirtualHost>
Changes to the "/etc/httpd/conf/httpd.conf" file will not take effect until the httpd service is reloaded or restarted.
# OL6 service httpd reload # OR service httpd restart # OL7+ systemctl reload httpd # OR systemctl restart httpd
Remember, for named virtual hosts to work, the URL must contain the correct name, so to test this you will either need the appropriate DNS entries, or "/etc/hosts" entries. In my case the reverse proxy is running on a server with an IP address of "192.168.0.190", so the hosts file would look like this.
192.168.0.190 my-app-1.example.com 192.168.0.190 my-app-2.example.com
The two applications are now being proxied using the following URLs.
http://my-app-1.example.com http://my-app-2.example.comAn alternative is to proxy based on a sub-directory, making the DNS management for multiple applications a little simpler. The following "/etc/httpd/conf/httpd.conf" file configuration shows an example of this.
ProxyRequests Off
<VirtualHost 192.168.0.190:80>
ServerName www.example.com
ServerAlias example.com
ErrorLog /var/log/httpd/example-error_log
TransferLog /var/log/httpd/example-access_log
ProxyPass /my-app-1/ http://app-server-1.localdomain:7002/
ProxyPassReverse /my-app-1/ http://app-server-1.localdomain:7002/
ProxyPass /my-app-2/ http://app-server-1.localdomain:7004/
ProxyPassReverse /my-app-2/ http://app-server-1.localdomain:7004/
</VirtualHost>
This method requires a single DNS or hosts file entry.
192.168.0.190 www.example.comThe following URLs would be proxied to the appropriate server(s).
http://www.example.com/my-app-1/ http://www.example.com/my-app-2/
HTTPS Reverse Proxy
In order to define a HTTPS reverse proxy you will need to configure Apache to handle HTTPS requests. You can see how to do this here. The following examples rely on this configuration.
The HTTPS reverse proxy definitions are similar to those seen previously, with the addition of the SSL related parameters. The following example also includes redirects to make sure any HTTP requests are redirected to HTTPS.
ProxyRequests Off
NameVirtualHost *:80
NameVirtualHost *:443
SSLProtocol ALL -SSLv2 -SSLv3
SSLHonorCipherOrder On
SSLCipherSuite ECDHE-RSA-AES128-GCM-SHA256:ECDHE-ECDSA-AES128-GCM-SHA256:ECDHE-RSA-AES256-GCM-SHA384:ECDHE-ECDSA-AES256-GCM-SHA384:DHE-RSA-AES128-GCM-SHA256:DHE-DSS-AES128-GCM-SHA256:kEDH+AESGCM:ECDHE-RSA-AES128-SHA256:ECDHE-ECDSA-AES128-SHA256:ECDHE-RSA-AES128-SHA:ECDHE-ECDSA-AES128-SHA:ECDHE-RSA-AES256-SHA384:ECDHE-ECDSA-AES256-SHA384:ECDHE-RSA-AES256-SHA:ECDHE-ECDSA-AES256-SHA:DHE-RSA-AES128-SHA256:DHE-RSA-AES128-SHA:DHE-DSS-AES128-SHA256:DHE-RSA-AES256-SHA256:DHE-DSS-AES256-SHA:DHE-RSA-AES256-SHA:AES128-GCM-SHA256:AES256-GCM-SHA384:AES128-SHA256:AES256-SHA256:AES128-SHA:AES256-SHA:AES:CAMELLIA:DES-CBC3-SHA:!aNULL:!eNULL:!EXPORT:!DES:!RC4:!MD5:!PSK:!aECDH:!EDH-DSS-DES-CBC3-SHA:!EDH-RSA-DES-CBC3-SHA:!KRB5-DES-CBC3-SHA
# Redirect HTTP requests to HTTPS
<VirtualHost *:80>
ServerName my-app-1.example.com
ServerAlias my-app-1
Redirect / https://my-app-1.example.com/
</VirtualHost>
# Redirect HTTP requests to HTTPS
<VirtualHost *:80>
ServerName my-app-2.example.com
ServerAlias my-app-2
Redirect / https://my-app-2.example.com/
</VirtualHost>
<VirtualHost *:443>
ServerName my-app-1.example.com
ServerAlias my-app-1
ErrorLog /var/log/httpd/my-app-1-error_log
TransferLog /var/log/httpd/my-app-1-access_log
ProxyPass / http://app-server-1.localdomain:7002/
ProxyPassReverse / http://app-server-1.localdomain:7002/
SSLEngine On
SSLProxyEngine On
SSLCertificateFile /etc/pki/tls/certs/www.example.com
SSLCertificateKeyFile /etc/pki/tls/private/www.example.com
#SSLCACertificateFile /etc/pki/tls/certs/intermediate.crt
</VirtualHost>
<VirtualHost *:443>
ServerName my-app-2.example.com
ServerAlias my-app-2
ErrorLog /var/log/httpd/my-app-2-error_log
TransferLog /var/log/httpd/my-app-2-access_log
ProxyPass / http://app-server-1.localdomain:7004/
ProxyPassReverse / http://app-server-1.localdomain:7004/
SSLEngine On
SSLProxyEngine On
SSLCertificateFile /etc/pki/tls/certs/www.example.com
SSLCertificateKeyFile /etc/pki/tls/private/www.example.com
#SSLCACertificateFile /etc/pki/tls/certs/intermediate.crt
</VirtualHost>
Notice the "SSLCACertificateFile" entry is commented out. If you are using a real certificate, you will probably need to download the intermediate bundle from the CA and reference it using this tag.
After a restart of the httpd service, the following URLs will be proxied appropriately.
http://my-app-1.example.com (redirected to HTTPS) https://my-app-1.example.com http://my-app-2.example.com (redirected to HTTPS) https://my-app-2.example.com
The following is a HTTPS equivalent of the sub-directory reverse proxy shown in the previous section.
ProxyRequests Off
SSLProtocol ALL -SSLv2 -SSLv3
SSLHonorCipherOrder On
SSLCipherSuite ECDHE-RSA-AES128-GCM-SHA256:ECDHE-ECDSA-AES128-GCM-SHA256:ECDHE-RSA-AES256-GCM-SHA384:ECDHE-ECDSA-AES256-GCM-SHA384:DHE-RSA-AES128-GCM-SHA256:DHE-DSS-AES128-GCM-SHA256:kEDH+AESGCM:ECDHE-RSA-AES128-SHA256:ECDHE-ECDSA-AES128-SHA256:ECDHE-RSA-AES128-SHA:ECDHE-ECDSA-AES128-SHA:ECDHE-RSA-AES256-SHA384:ECDHE-ECDSA-AES256-SHA384:ECDHE-RSA-AES256-SHA:ECDHE-ECDSA-AES256-SHA:DHE-RSA-AES128-SHA256:DHE-RSA-AES128-SHA:DHE-DSS-AES128-SHA256:DHE-RSA-AES256-SHA256:DHE-DSS-AES256-SHA:DHE-RSA-AES256-SHA:AES128-GCM-SHA256:AES256-GCM-SHA384:AES128-SHA256:AES256-SHA256:AES128-SHA:AES256-SHA:AES:CAMELLIA:DES-CBC3-SHA:!aNULL:!eNULL:!EXPORT:!DES:!RC4:!MD5:!PSK:!aECDH:!EDH-DSS-DES-CBC3-SHA:!EDH-RSA-DES-CBC3-SHA:!KRB5-DES-CBC3-SHA
# Redirect HTTP requests to HTTPS
<VirtualHost 192.168.0.190:80>
ServerName www.example.com
ServerAlias example.com
Redirect / https://www.example.com/
</VirtualHost>
<VirtualHost 192.168.0.190:443>
ServerName www.example.com
ServerAlias example.com
ErrorLog /var/log/httpd/example-error_log
TransferLog /var/log/httpd/example-access_log
ProxyPass /my-app-1/ http://app-server-1.localdomain:7002/
ProxyPassReverse /my-app-1/ http://app-server-1.localdomain:7002/
ProxyPass /my-app-2/ http://app-server-1.localdomain:7004/
ProxyPassReverse /my-app-2/ http://app-server-1.localdomain:7004/
SSLEngine On
SSLProxyEngine On
SSLCertificateFile /etc/pki/tls/certs/www.example.com
SSLCertificateKeyFile /etc/pki/tls/private/www.example.com
#SSLCACertificateFile /etc/pki/tls/certs/intermediate.crt
</VirtualHost>
The after a restart of the httpd service, the following URLs will be proxied appropriately.
http://www.example.com/my-app-1/ (redirected to HTTPS) https://www.example.com/my-app-1/ http://www.example.com/my-app-2/ (redirected to HTTPS) https://www.example.com/my-app-2/
For more information see:
- Linux HTTP Server Configuration
- Apache Tomcat Installation on Linux
- Apache Monitoring using mod_status (server-status)
- NGINX : Reverse Proxy Configuration
- Let's Encrypt - Free Certificates on Oracle Linux (CertBot)
- Server Icon
- Cloud Icon
Hope this helps. Regards Tim...